Firewall deployment sounds straightforward until you’re in the middle of a cutover window, a critical app starts timing out, and everyone asks the same question: “Why didn’t we catch this earlier?”
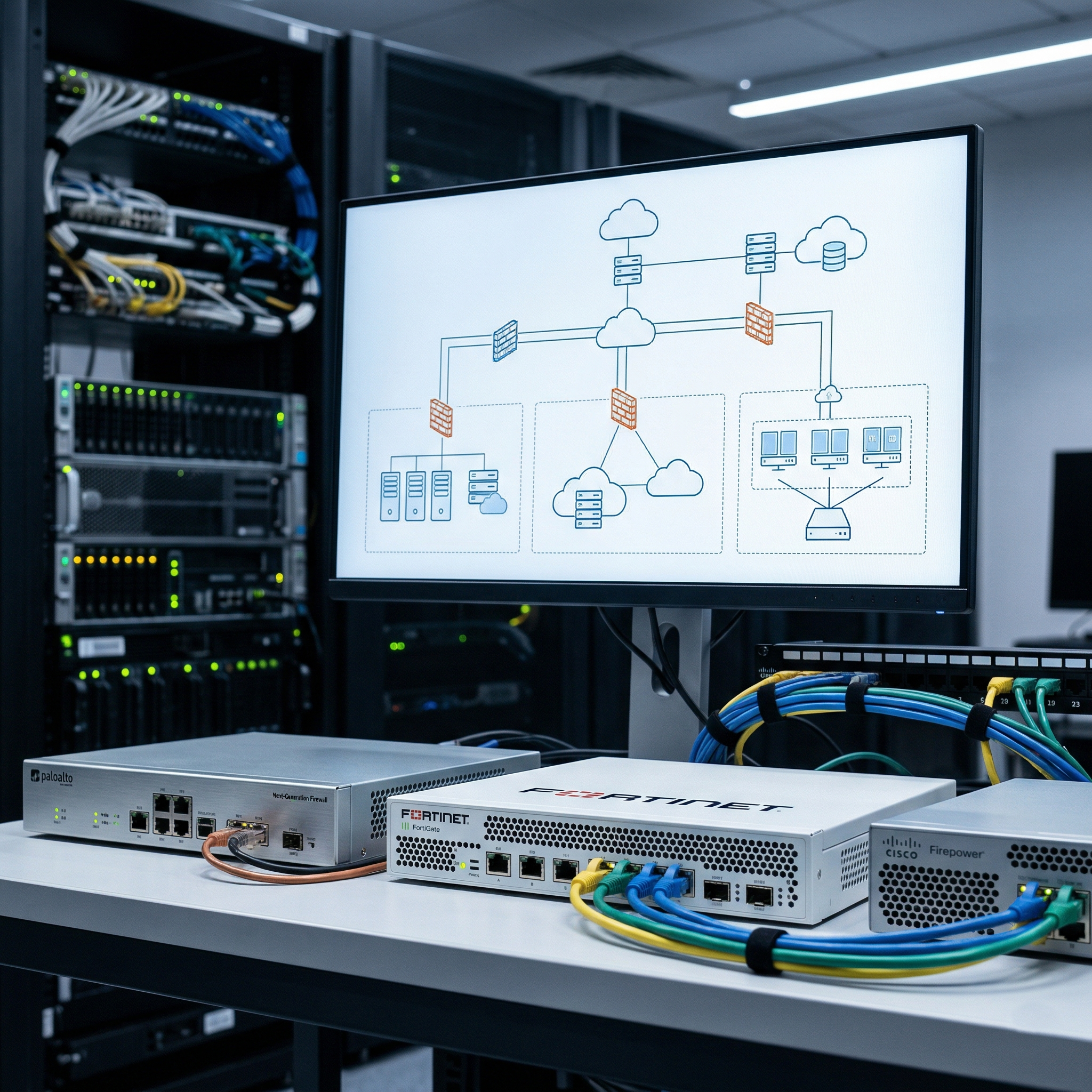
If you’re planning Firewall Deployment globally, across branches, data centers, remote users, and cloud workloads, the platform you pick matters, but the deployment approach matters more. Palo Alto, Fortinet, and Cisco can all secure modern networks, but they differ in how you design policy, roll out changes, manage scale, and troubleshoot issues at 2 a.m.
This guide compares real-world deployment considerations, not marketing slides, and ends with a practical checklist you can use before you go live.
What “next-gen firewall deployment” really includes
A proper next-gen firewall rollout is more than swapping a box.
It usually includes:
- Network and application discovery (what actually talks to what)
- Policy design (zones, segmentation, least privilege rules)
- VPN or secure access setup for users and sites
- SSL/TLS inspection decisions (what to decrypt, what to exclude)
- Logging and monitoring (SIEM/SOC handoff, alert tuning)
- High availability (HA) and failover testing
- Cutover plan plus rollback plan
- Post-go-live rule cleanup and optimization
The firewall brand changes the tools and workflow. The outcome depends on how disciplined your implementation is.
Quick comparison: Palo Alto vs Fortinet vs Cisco
Here’s a simple way to frame it:
- Palo Alto Networks: strong application visibility and policy control, popular in enterprises with complex segmentation needs.
- Fortinet (FortiGate): fast value, strong performance for price, widely used for branch + SD-WAN style rollouts.
- Cisco (Secure Firewall and ecosystem): fits well when you’re already a Cisco shop and want tight integration with Cisco networking, identity, and security tooling.
All three can do NGFW basics like app control, IPS, VPN, and URL filtering. The differences show up in day-to-day management, scaling globally, and how cleanly you can standardize deployments.
Deployment fit: which environments each platform handles best
1) Global branches and remote offices
- Fortinet tends to shine for repeatable branch deployments, templates, and performance per dollar, especially when SD-WAN is part of the plan.
- Palo Alto can be great here too, but it’s often chosen when security policy complexity is high (strict segmentation, heavy app-based rules).
- Cisco can fit well when your branch stack is already Cisco-heavy (switching, routing, WAN), and you want fewer vendors.
Practical tip: If you have 50 to 500 branches, the “how fast can we standardize builds and push changes safely?” question becomes more important than feature checkboxes.
2) Data center segmentation (east-west control)
- Palo Alto is often selected for granular app-based controls and segmentation strategies that evolve over time.
- Cisco can be strong when paired with Cisco identity/network segmentation approaches in Cisco-led architectures.
- Fortinet is used in data centers as well, especially when cost and throughput are key, and your policies are consistent and template-friendly.
Practical tip: For data centers, don’t skip baseline traffic mapping. Most “firewall broke the app” issues are really “we never documented the dependencies.”
3) Hybrid cloud (AWS/Azure + on-prem)
All three vendors have cloud options and patterns for deploying in public cloud, but your decision should also consider:
- How you’ll maintain policy consistency between on-prem and cloud
- Whether you need centralized management across regions
- Whether you’ll shift toward SASE/Zero Trust access for users over time
Practical tip: For cloud-heavy orgs, you may get better outcomes by combining NGFW with SASE/secure access rather than forcing every use case through a traditional perimeter model.
Policy design differences that affect your rollout
Policy is where most deployments win or fail.
Palo Alto: app-first policy culture
Palo Alto deployments often become cleaner when teams use:
- App-ID driven rules
- User-ID where it makes sense
- Strong object/tag discipline
If your team is ready to invest time in policy design, you can end up with a rulebase that’s easier to reason about.
Fortinet: fast rollout, strong templates, careful with sprawl
Fortinet is often praised for speed and repeatability, but like any platform, if you move fast without governance, you can end up with:
- Too many broad rules
- Inconsistent objects across sites
- “Temporary” policies that become permanent
Cisco: ecosystem-aligned policies
Cisco deployments can be smoother when you align firewall policy with:
- Your identity strategy
- Your network segmentation design
- Existing Cisco monitoring and security tools
The best Cisco outcomes usually happen when the firewall isn’t treated as a standalone island.
A small decision table you can use internally
Decision factor | Palo Alto | Fortinet | Cisco |
App-level policy control | Strong | Strong | Strong |
Branch rollout repeatability | Good | Very strong | Good |
Best fit when you already use vendor ecosystem | Neutral | Neutral | Strong if Cisco-heavy |
Cost efficiency at scale | Medium | Strong | Medium |
Complex segmentation programs | Strong | Good | Good (depends on architecture) |
Use this as a starting point, then validate with a short proof-of-concept that matches your real traffic.
The deployment checklist that prevents cutover pain
Use this before you schedule a go-live.
Step 1: Document the flows (don’t guess)
- List critical apps and owners
- Map source, destination, ports, and protocols
- Identify SaaS dependencies (auth, APIs, payment gateways)
- Confirm DNS, NTP, certificate dependencies
Step 2: Design zones and segmentation early
- Define trust boundaries (user, server, DMZ, guest, OT, cloud)
- Create naming standards for objects and groups
- Decide how exceptions will be requested and approved
Step 3: Build policies from “allow list” thinking
- Start tight for crown-jewel apps
- Avoid “Any-Any” rules as placeholders
- Add temporary rules with an expiry date and ticket reference
Step 4: Decide SSL inspection scope
- Choose what to decrypt (high-risk categories, unknown apps)
- Exclude sensitive traffic where required (banking, healthcare portals, privacy needs)
- Validate certificates and client compatibility
Step 5: Logging and SOC readiness
- Turn on logs for allowed and blocked traffic (at least at rollout)
- Forward logs to SIEM
- Tune alerts so the SOC isn’t buried on day one
- Set clear escalation paths (who responds, when, and how)
Step 6: HA and rollback are non-negotiable
- Test failover during a controlled window
- Confirm config sync behavior
- Create a rollback plan that’s actually executable in minutes
Step 7: Run a realistic test plan
- Test critical user journeys (login, checkout, file upload, video calls)
- Validate VPN/remote access
- Confirm latency-sensitive apps behave normally
- Compare performance baselines before and after
Common deployment mistakes (and how to avoid them)
- Mistake: Migrating rules without cleanup
Fix: Remove unused rules first, then migrate. A messy policy stays messy after migration. - Mistake: No ownership of applications
Fix: Assign an owner per critical app for testing and sign-off. - Mistake: Turning on everything at once
Fix: Phase features. Example: go live with core policy + IPS, then add SSL inspection once stable. - Mistake: No change control discipline
Fix: Use staged changes, peer review, and documented rollback steps. - Mistake: Ignoring operational workload
Fix: Plan who manages day-two tasks: rule requests, log review, updates, incident response.
Managed deployment vs in-house: what most teams overlook
Even experienced IT teams get stretched during firewall projects. The hidden load is:
- Rule review cycles
- App testing coordination
- Log tuning
- Post-deployment optimization
- Documentation for audits and compliance
If you’re rolling out globally, it’s often worth using an implementation partner for planning, migration, and validation, then deciding what you keep in-house for day-to-day operations.
When to talk to Cylentrix
If you’re comparing Palo Alto vs Fortinet vs Cisco and want a deployment that doesn’t end in firefighting, Cylentrix can help you:
- Choose the right platform for your environment and growth plan
- Design clean zones, segmentation, and least-privilege policy
- Migrate safely from legacy firewalls with minimal downtime
- Integrate logging with SIEM and 24/7 monitoring workflows
- Test HA, failover, VPN, and business-critical applications before go-live
If you want a rollout plan you can trust, talk to us and we’ll map your requirements, recommend a practical deployment approach, and help you execute it end-to-end.
FAQs
1) Which firewall is best for global deployments?
It depends on your sites, cloud usage, and how standardized you want operations to be, but all three can work well when paired with strong templates and governance.
2) Do I need SSL inspection in my firewall deployment?
Not always for day one. Many teams go live without it, stabilize traffic, then enable SSL inspection in phases to avoid breaking applications.
3) How long does a typical firewall deployment take?
Small deployments can be done in days, while multi-site enterprise rollouts often take weeks or months due to discovery, testing, and change windows.
4) Should I migrate rules as-is from my old firewall?
Usually no. Clean up and rationalize first, or you’ll carry old risk and clutter into the new platform.
5) What’s the most important success factor in firewall deployment?
Testing and rollback planning. If you can validate critical flows and reverse changes fast, your risk drops dramatically.